Auto-ID technology is implemented in several different ways, including barcodes, lasers, voice recognition and biometrics. These techniques suffer from limitations such as the need for line-of-sight (LOS) with the interrogator (lasers and barcodes), low data storage capacities (barcodes) and the need for human intervention (voice recognition and biometrics).
Radio Frequency Identification (RFID) was developed to overcome these limitations. RFID provides an Auto-ID technology that does not require LOS, has a longer read range, can store large amounts of user data using integrated technology and allows changes to the stored data. RFID proves useful when traceability through process or life cycles is required; where data errors are high, such as in material identification or handling; and where business systems need more information than automatic identification technologies like bar coding can provide.
RFID is one of the most promising, rapidly developing, convenient, easy-to-use technologies, which uses radio frequency (RF) signals for automatic identification of objects/items. It offers the advantage of read/write (R/W) capability without being limited by line-of-sight type of propagation, can function under a variety of environmental conditions, provides a high level of data integrity and high level of security.1-3 RFID enables machine-to-machine communication and event driven communication, where data is provided and processed in real time.4 RFID, using the simplest form of electronics, is available in a choice of form and function that is virtually limitless.
History and Benefits of RFID
Although RFID found implementation in tracking supplies in the late 1980s, it has been in existence since 1939,5,6 when it was first used as an Identify Friend or Foe (IFF) technique in World War II to identify whether airplanes were friend or foe, during night operations by the British Royal Air Force.
Another early work exploring RFID is the landmark 1948 paper by Harry Stockman,7 who predicted that “...considerable research and development work has to be done before the remaining basic problems in reflected-power communication are solved and before the field of useful applications is explored.”
In the 1960s and 1970s, RFID tags found military applications such as equipment and personnel tracking8,9 and some unique commercial applications such as identification and temperature sensing of cattle. The technology has now evolved for use in the railroad industry to track railroad cars, in the automotive industry for automation and tracking purposes, in agriculture and wildlife management to track livestock and wildlife, and in retail as an anti-theft device.
Mario Cardullo claims that his 1973 US Patent 3,713,148, a passive radio transponder with memory, was the first true ancestor of modern RFID. The first demonstration of today’s reflected power (backscatter) RFID tags were done at the Los Alamos Scientific Laboratory in 1973.6 However, the major development in RFID tracking came only in the 1980s and 1990s, when industrial goods needed counterfeit protection, shrinkage protection and tracking through the several stages in the supply chain. In the 1980s, Compaq computer started using RFID tags to trace components through the production process. RFID technology prevents theft or counterfeiting of goods, thus providing security, automatic counting of goods that enter or leave warehouses, thus allowing to keep track of the stock levels. Passive UHF RFID systems are increasingly being employed in distribution and supply chains.
The initial benefits of RFID in a warehouse or distribution center environment are mainly derived from automating manual processes and effectively using greater amounts of data. For example, using RFID tags to automate the receiving operation can reduce the labor cost for that function, as well as enhance accuracy and help decrease the amount of time that a carton spends in a distribution center. All the benefits of using an RFID system depend on the varying levels of RFID use, from pallet tagging to item tagging. At the pallet tagging level, RFID offers improvements in product diversion, production planning, inventory control and storage, and vendor-managed inventory programs, among other places. At the case tagging level, RFID presents opportunities for improved demand and supply planning, theft identification, and pick, pack and ship control. In item tagging, RFID allows a variety of benefits, including store-level promotions and pricing, item theft prevention, and capacity planning, among many others.2
RFID System Architecture
A typical RFID system is composed of the following four components, as shown in Figure 1.
Figure 1 Typical RFID system components.
RFID Tags or Transponders
Historically, an RFID device that did not actively transmit to a reader was known as a tag. An RFID device that actively transmits to a reader was known as a transponder (TRANSmitter + resPONDER). However, it has become common within the industry to interchange the terminology and refer to these devices as either tags or transponders.1,9
A tag’s performance parameters are its read range, transmission speed (data rate) and the impact caused by surrounding objects. The frequency, the orientation to the reader field, and the design and size of the antenna determine an RFID tag’s read range and its flexibility to environment factors. The frequency and the associated transmission protocol (anti-collision algorithm) determine the basic rate of data transmission.4
RFID tags are further divided into active and passive tags. An RFID device that uses a battery and actively transmits to a reader is termed an “active” tag. An RFID tag that only reflects or backscatters transmission from a reader is termed “passive”. In general, active tags use batteries to power the tag transmitter (radio) and receiver. Active tags are usually larger in size and more expensive than passive tags. The life of an active tag is directly related to battery life.
RFID Readers or Transceivers
The RFID reader or transceiver is the source of the RF energy used to activate and power the passive RFID tags. It transmits the RF signals, receives the encoded signal from the tag, decodes the tag’s identification and transmits the identification data to the host computer.1
The reader antenna establishes a connection between the reader electronics and the electromagnetic wave in the space. In the UHF range, reader antennas (like tag antennas) come in a variety of designs. Highly directional, high-gain antennas are used for large read distances. Regulatory authorities usually limit the maximum power emitted in a given direction (transmission power plus the antenna gain). The antenna gain is linked to the antenna size; the higher the gain (or smaller the solid angle into which the antenna emits), the larger the mechanical design of the antenna will be. Highly directional antennas are not used for handheld readers. Antennas typically used for handheld readers include patch antennas, half-wave dipoles and helix antennas. Larger antenna structures can be used for stationary readers. In the UHF range, they usually take the form of arrays. The size determines the far field of such antennas.4
RFID Middleware
RFID middleware connects the RFID reader layer to the business applications. Its task is to process RFID events and present them to the business applications in such a way that they can be processed further by those applications. The middleware also monitors the RFID hardware (readers, antennas and so on). This involves sending confirmations to the feedback providers and monitoring the sensors (light barriers, timers, motion detectors), since this cannot be combined initially with the casual process logic.4 The primary function of the RFID middleware is filtering, which is to read all the tags at a location ensuring that the same electronic product code (EPC) tags are not read over and over again.10
RFID Application Software
The RFID reader is connected to the host computer, which is used to program the reader and store information received from the transponder. As a result of a service-oriented architecture (SOA), software is configured and adapted for different applications. Software development tools can be used to organize the individual services in line with process requirements. Web services, Extensible Markup Language (XML), message queuing, and workflows are elements of an SOA and of RFID middleware that can be used to link different services.4
Working of RFID System
RFID is similar in concept to bar coding.1 Bar code systems use a reader and coded labels that are attached to an item, whereas RFID uses a reader and special RFID devices that are attached to an item. Bar codes use optical signals to transfer information from the label to the reader; RFID uses RF signals to transfer information from the RFID device to the reader.
Radio waves transfer data between an item to which a RFID device is attached and an RFID reader. The device can contain data about the item, such as what the item is, what time the device travelled through a certain zone, perhaps even a parameter such as temperature. RFID devices, such as a tag or label, can be attached to virtually anything, from a vehicle, as shown in Figure 2, to a pallet of merchandise. The reader and tag communicate using the antennas and a defined command set. The communication protocol is defined such that the reader first sends a command and the tag responds. The command set includes commands to read and write data, to control the anti-collision protocol, to lock individual memory cells, and to deactivate the tag (kill command).

Figure 2 An RFID tag used for electronic toll collection (source: www.wikipedia.com).
The classification of UHF RFID tags is also based on their operation and functionality,11,12 as detailed below:
- Class 0 - passive read only tags
They use out of band signaling and backscatter technique to communicate to the reader. - Class 1 - write-once-read-many (WORM) passive tags
The programming of the tags can be done by the manufacturer or by the user, but only once. The tags use in band signaling and backscattering. - Class 2 - additional storage capacity and encrypted passive tags
They use backscattering to communicate with each other. - Class 3 - semi passive tags
The tags have a battery source to operate the internal circuitry. However, they do not have a transmitter to send across signals to other tags/readers. They also use backscattering for reader communication. - Class 4 - active tags
The tags have battery source to supply power to the internal circuitry and have a transmitter too. These tags are also capable of communicating with other tags that have the same technology. - Class 5 - active tags with additional capability
The tags have the additional capability of successfully powering other ICs of peer class and lower classes and can have two-way communication with Class 4 tags. RFID readers come under this category.
Figure 3 illustrates how complex the flow of data can be through IT systems operating with RFID procedures. In this case, RFID data is fed via RFID middleware servers to a company’s central data center. The data center runs the conventional business applications, whereby distinguishing between central and local data management is needed. With central data management, only an object’s identification number is transferred (the information on the tag). Any other data associated with the object is stored in central databases.4
Figure 3 EPC global oriented RFID applications and communication structure (source: Oracle/GSI Germany).
The Savant™ system is a hierarchical control and data management building block that can be used to provide automated control functionality and manage the large volumes of data generated by the RFID readers. A Savant enables the distributed creation of a reader network by acting as a gateway to the next higher level in the Savant hierarchy, effectively isolating the reader sub-network. The use of Savants enables distributed security by providing convenient points for network isolation.
The Savant network further reduces the burden on the tags while providing several advantages. First, it reduces the memory and power requirements on the tags by transferring the computationally intensive functionality to a powered system. Second, it makes the system more robust; any single point of failure has local effects. Third, it enables the entire system to be scalable as systems and reader sub-networks may be added seamlessly. Finally, the Savant network significantly reduces the footprint of the tag’s microchip, reducing the cost of the transponder.3,13
Applications of RFID
RFID is used in applications such as:1,6
- Asset identification and tracking
- Electronic toll collection
- Railway car identification and tracking
- Access control
- Item management for retail, health care and logistics application
- Animal identification
- Fuel dispensing loyalty programs
- Automobile immobilizing (security) - central locking systems
RFID functions are also integrated in passports of many countries, including Malaysia, Germany, the UK and the US, and is used in transportation systems for payments in many parts of the world—New York City subway, Moscow Metro, UK public transport, Taiwan transportation system, Hong Kong, Paris public transport system, Western Australia Transperth public transport network, etc. RFID tags will soon be on our health cards.
Figure 4 shows a nearly perfect supply chain visibility, which eliminates human error from data collection, reduces inventories, keeps product in-stock, reduces loss and waste, and improves safety and security.14 Most RFID applications are currently found in “closed” processes, where the tags are reused time and again and within one organization or company. One example of ‘closed loop’ is in a library to register the books on loan and in areas requiring document management. The retail industry usually operates “open” systems with labels on the packaging that are discarded at the end, together with the RFID tags. Such cases are referred to as ‘open loop’.4
Figure 4 Supply chain using an RFID system (source: www.ficci.com).
RFID Standards
EPCglobal Inc., a division of GS1 (Global Standards 1 is an organization created by combining the former UCC and EAN organizations), has developed a new Electronic Product Code (EPC) as the next standard for tracking products through the supply chain. EPC utilizes the basic structures of the Global Trade Item Number (GTIN) and Serialized Shipping Container Code (SSCC), as well as others.15 EPCglobal Inc. has also defined a global protocol operating in the UHF range for carton and pallet labeling. This protocol, referred to as EPC Class 1 Generation 2 (or “Gen 2”), will replace several older Class 1 protocols that did not provide global interoperability.
While EPCglobal focuses mainly on open-loop supply chain tracking application, ISO (The International Organization for Standardization) has many RFID protocols defined at various frequencies and for numerous applications, as shown in Table 1. The 18000 standards describe measurement procedures for checking RFID structures.3,4,16
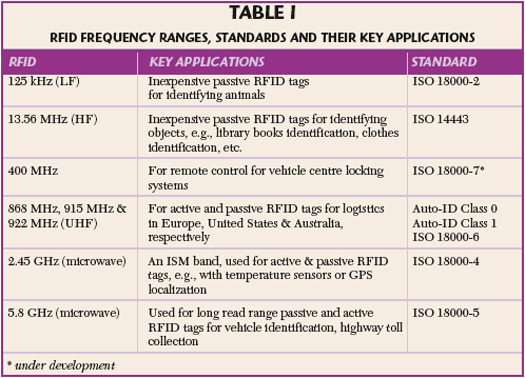
Table 1 RFID Frequency Ranges, Standards, and Their Key Applications
The Electronic Product Code (EPC)
The EPC is a 96-bit number made up of a header and three sets of data. There are several iterations of the EPC, depending upon the specific application. EPC is currently the most common encoding scheme for warehouse and distribution applications. EPC tags can be active or passive, read-only or read-writable. An example of a typical EPC code is shown in Figure 5. The header identifies the EPC version number, which identifies the type of EPC data to follow. The second part of the number identifies the EPC manager; typically, it is the manufacturer of the item the EPC is attached to. The third part is called object class and refers to the exact type of product—stock-keeping unit (SKU). The fourth series of numbers is the serial number that is unique to the item.15 A 96-bit EPC will allow sufficient capacity for 268 million companies. Each manufacturer will have the ability to create up to 16 million object classes with 68 billion serial numbers in each class.

Figure 5 Typical EPC code (source: www.paxar.com).
RFID Industry: Large and Unknown
Not all industries are expected to be equally likely to adopt RFID technologies. Some industries (like consumer electronics, pharmaceuticals and toys) are likely to rollout their implementations earlier due to suitable product attributes and category economics.
In June 2003, Wal-Mart greatly advanced the process of adoption when it announced that starting in January 2005, 100 of its top suppliers would need to tag all pallets and cases going to some Wal-Mart warehouses. Wal-Mart began its RFID pilot project on April 30, 2004. The eight suppliers that started shipping a handful of RFID-enabled pallets were Gillette, Hewlett-Packard, Johnson & Johnson, Kimberly-Clark, Kraft Foods, Nestle Purina Petcare, Procter & Gamble and Unilever. The Department of Defense (DoD), Target and Albertsons announced their future RFID-tagging requirements to their suppliers.4,12,17,18
Recently, several companies across the drug supply chain have been testing RFID deployment. European giants, such as Marks & Spencer and Tesco, have started piloting RFID tags in clothing, CDs and DVDs. In Australia, Coles Myer started a pilot in-house RFID trial in May 2004, which involves moving cages from one distribution center onto a truck then onto a receiving dock that the equipment recognises.
Market analysts, like Frost and Sullivan and ARC Advisory Group, expect the use of passive UHF RFID in manufacturing supply chain applications to achieve phenomenal growth over the next five years. Researchers predict that worldwide revenues from RFID transponders will jump to $2.8 B in 200919 and will be a $20 B market by 2013.12 According to Gartner, the use of RFID to capitalize on data flow in global supply chains could be one of the most significant developments since enterprises first explicitly recognized the importance of information flow in the supply chain.
RFID Security Aspects
In terms of security, RFID tags are inherently less secure, mainly because of the lack of processing capacity on these devices to handle much more than their core functions. RFID data must be used in compliance with clear regulations concerning IT security as well as consumer and data protection. An RFID system is usually limited to the RFID tags, the reader and the data transferred in this space (air interface). It might also include the threshold between the reader and the middleware that processes the data recorded. This means that when implementing an RFID system and designing its security concept, one has to ensure that the middleware and back-end systems are suitably safeguarded.20
The basic rule of thumb, however, is that simple RFID systems should store and transmit minimal amounts of data and that the application only gets its ‘intelligence’ from the RFID data in the back-end systems. As long as only manufacturer and serial numbers are transferred and cannot be turned into usable information without a combination of detailed information from the back-end systems, the security risk posed by the use of RFID can be deemed negligible.4
Challenges for RFID System: Physical Limitation, Technical Glitch, Cost, Standards and Consumer Concerns
The readability of the tags is heavily dependent on the materials, the structure and the places where the tags are located. For instance, it is very difficult to read a UHF tag if it is surrounded by metallic objects, liquids, or other highly conductive or reflective materials. Sometime a tag must be affixed to the outside of a batch (on a pallet, for example). It may be covered at most by paper, expanded polystyrene, or similar materials.4
So far, one technical hitch2 in introducing global RFID standards into Australia has been the level of power that reading devices can transmit on the designated 900 MHz bandwidth, as Australian devices have been restricted to using only one watt of power with a range of three to four meters. The standard in the US is four watts.
RFID is still more expensive than barcode technology. Figure 6 shows the RFID Timeline, as the RFID performance curve climbs to the right, there is a point at which the performance, or benefit, provided by using RFID tags begins to exceed the cost of the tags. It is at this point that adoption of RFID potentially begins to make business sense. As RFID is widely adopted, the cost of tags will fall in typical supply-demand fashion and RFID implementation that is too expensive today may become affordable in a matter of time.2

Figure 6 RFID timeline (source: FXI Logistex, 2006).
RFID standards are evolving and are still in an infant stage. Consumers are concerned about the abuse of the system and that this will have a negative effect on them, especially in regards to their privacy. Also, consumers are concerned about the health effects of the network’s radio waves.12,17 While these and other challenges would be tackled as the technology advances and moves closer to the mainstream, in the interim they will slow down the adoption process.
Conclusion
RFID is expected to provide huge advantages to manufacturers by offering the tools to better plan production and respond more quickly to market demand. It will facilitate automation of inventory counts and speed shipping and receiving at the distribution level.15 For retailers, it will help reduce stock-outs, enable product tracking and potentially reduce theft and streamline the point of sale (POS) function.
The Massachusetts Institute of Technology has coined the phrase ‘The Internet of Things’ to describe the vision of a future where Thing-to-Thing (T2T) communication takes place. Cradle-to-grave tracking of items without human intervention—the domestic freezer re-ordering supplies directly from the supermarket and the food telling the microwave how to cook it—are the kinds of uses that are already being considered for commercial applications. Just how far RFID goes is a question of tagging economics and time.22
While RFID technology offers a variety of potential benefits and advantages over current barcode technology and would eventually replace it, the technical, financial and psychological challenges have prevented it from attaining wide use in warehouse and distribution center operations. In the near future, while RFID technology strives to overcome these limitations and gain wider implementation, hybrid barcode-RFID systems will be the norm. However, taking into account the challenges and hurdles of exiting RFID technology, success will be more likely with short, well-defined and targeted projects. The 5 cents tag, as it has been called, has been widely viewed as the inflection point where wide adoption of RFID will quickly occur.3,23
Like so many other aspects of the business world, the enormous impact of Wal-Mart’s buying power will dictate how and when consumer goods companies adopt RFID technology. Wal-Mart’s impact in the marketplace has been the major impetus for the current buzz about RFID and will spur early adoption. Wal-Mart had a similar impact when they began using barcodes in the 1980s.12 But Wal-Mart could not have made their decision if many other factors, such as the back-end infrastructure, cost and standard, were not already in place. Companies like Wal-Mart, Tesco, Metro Group, Target and Albertsons will not be able to scale to a trillion dollars in revenue using the limited information provided by barcodes. They have to do it with the next generation of technology, and that is going to be RFID.2,19 The early successes will not only help an organization, but they will also lay the groundwork for successful future investment in the technology.
References
- Intermec Technologies Corp., “RFID Overview: Introduction to Radio Frequency Identification,” RFID Journal, 2006.
- FKI Logistex, “RFID for the Real World,” RFID Journal, 2006.
- “RFID FAQs,” RFID Journal, http://www.rfidjournal.com.
- Radio Frequency Identification from Wikipedia, http://en.wiki pedia.org/wiki/Rfid.
- Symbol Technology, “Understanding the Key Issues in Radio Frequency Identification (RFID),” Whitepaper, 2004.
- Bitkom, “RFID: Technology, Systems and Applications,” Whitepaper, 2005.
- H. Stockman, “Communications by Means of Reflected Power,” Proceedings of the IRE, Vol. 36, No. 10, October 1948, pp. 1196-1204.
- J. Eagleson, “RFID: The Early Years 1980—1990,” 2002, http://members.surfbest.net/eaglesnest/rfidhist.htm.
- K. Finkenzeller, RFID Handbook, Second Edition, John Wiley & Sons Inc., Hoboken, NJ, 2003.
- TR3 Solutions, “Top 10 Myths about RFID Data Analytics,” RFID Journal, 2006.
- S. Sarma and D.W. Engels, “On the Future of RFID Tags and Protocols,” Whitepaper, Auto-ID Center, Massachusetts Institute of Technology, 2003.
- RedPrairie, “RFID Technology,” http://www.idspackaging.com.
- S. Sarma and D.W. Engels, “RFID Systems, Security and Privacy Implications,” Whitepaper, Auto-ID Center, Massachusetts Institute of Technology, 2002.
- R. Mathur, “Standardization: Key to Collaboration and Success,” EAN India, http://www.ficci.com.
- Paxar, “RFID Basics Updated,” RFID Journal, 2006.
- D. Reigelsperger and J. Harkins, “Keeping Pace with RFID,” http://www.lowrycomputer.com.
- EAI Technologies, “Realizing the Promise of RFID: Insights from Early Adopters and the Future Potential,” Whitepaper, 2005.
- Info Guide to RFID Technology, http://www.rfid-101.com.
- RFID Gazette, “RFID Tag Revenues to Increase 800%,” http://www.rfidgazette.org.
- BSI Study, “Security Aspects and Prospective Applications of RFID Systems,” p. 45.
- M. Crawford, “Retail Group Supports RFID Code of Practice,” 2004, http://www.computerworld.com.au.
- P. Harrop, “Tracking New Markets with Radio Frequency ID (RFID) Tags,” http://www.synopsys.com.
- M. Bhuptani and S. Moradpour, “Emerging Trends in RFID,” 2005, http://www.phptr.com.
